
Gatekeeper in MacOS is now stricter than ever, defaulting to only allow options for apps downloaded from either the App Store or the App Store and identified developers. Advanced Mac users may wish to allow a third option, which is the ability to open and allow apps downloaded from anywhere in macOS Sierra, macOS High Sierra, and MacOS Mojave.
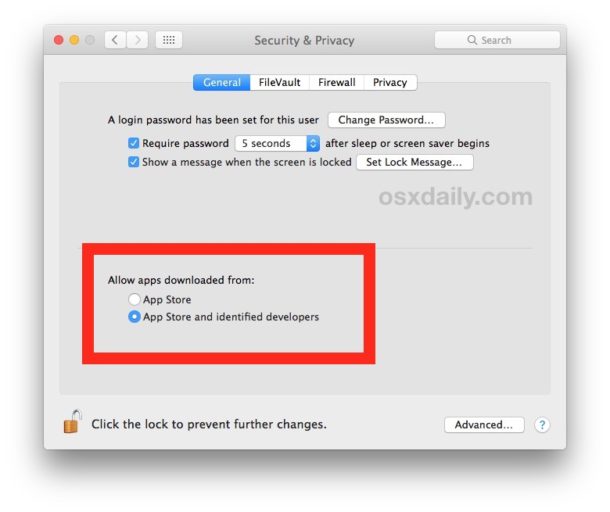
To be clear, the “Allow applications downloaded from anywhere” option is hidden by default in Gatekeeper for macOS from Sierra onward. You can see this by going to the Security & Privacy preference panel, and under the “General” section you will not find such an option for Gatekeeper app allow settings. Despite that, with a little command line intervention you can reveal the third option and regain the ability to open apps that come from anywhere.
This is not recommended for most Mac users, only advanced Mac users and developers who have the ability to accurately gauge app validity should use this method, which involves disabling Gatekeeper from the command line, thereby removing the standard Gatekeeper security mechanisms in Mac OS.
How to Allow Apps from Anywhere in Gatekeeper for macOS Mojave, MacOS Sierra
Quit out of System Preferences
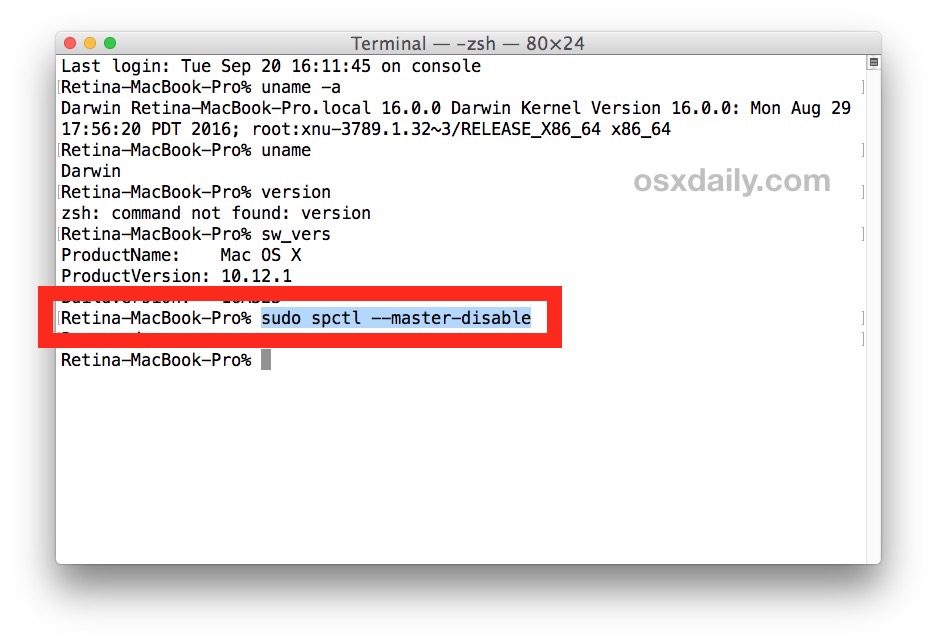
Open the Terminal app from the /Applications/Utilities/ folder and then enter the following command syntax:
sudo spctl --master-disable
Hit return and authenticate with an admin password
Relaunch System Preferences and go to “Security & Privacy” and the “General” tab
You will now see the “Anywhere” option under ‘Allow apps downloaded from:’ Gatekeeper options 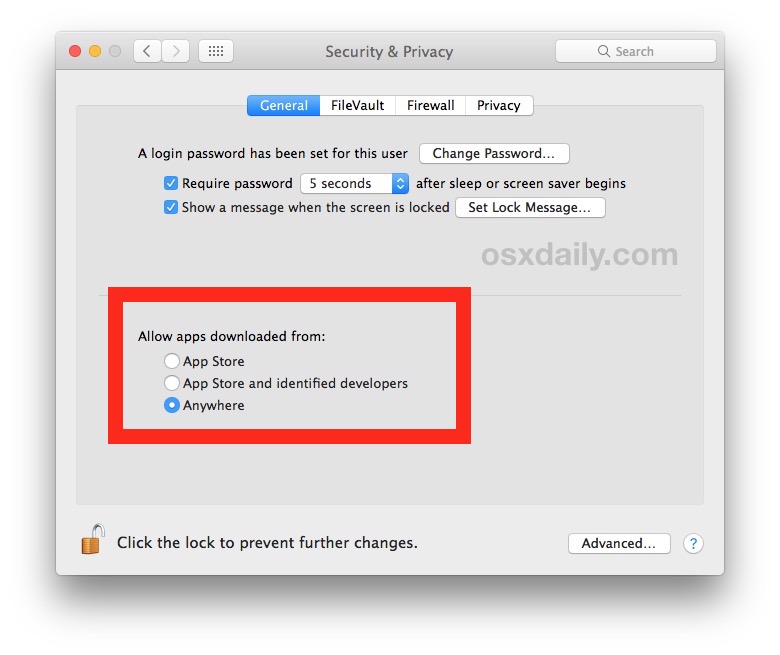
You’ll now be able to open and launch apps from anywhere under macOS Mojave, High Sierra, and Sierra, but be forewarned this turns off Gatekeeper and is not recommended for the vast majority of Mac users.
Allowing apps from anywhere including unidentified developers can potentially leave a Mac vulnerable to certain malware and junkware and should be avoided by all Mac users with the exception of those with genuinely advanced abilities.
Another approach is to manually add Gatekeeper exceptions via the command line, a solution which may be more appropriate than simply allowing everything to skirt past Gatekeeper.
Returning to Default Gatekeeper Security in macOS Mojave, High Sierra, Sierra
You can also reverse this and go back to the default strict Gatekeeper settings of only allowing apps from the Mac App Store and identified developers by issuing the following command string:
sudo spctl --master-enable
Hitting return and re-authenticating will return macOS Gatekeeper back to its strict default state of disallowing random apps from launching.
Nearly every Mac user should leave this feature enabled in the default state. If you do not have the ability to easily discern which apps are legitimate or not, you should absolutely not change this option. The “app can’t be opened because it is from an unidentified developer” message is there to offer protection to the vast majority of Mac users and should not be ignored.
Similar Posts:
- [Solved] PANIC: Missing emulator engine program for ‘x86’ CPUS.
- [Solved] IOS Package Error: ARCHIVE FAILED:Command CodeSign failed with a nonzero exit code
- error: command ‘gcc’ failed with exit status 1 [How to Solve]
- Download the APK installation file of the free app directly from the Google play store
- Django Run Error: RuntimeError: maximum recursion depth exceeded while calling a Python object
- Solutions to xadmin’s “apps are’t loaded yet” error
- [Solved] RuntimeError: Model class apps.users.models.UserProfile doesn’t declare an explicit app_label and isn’t in an application in INSTALLED_APPS.
- django.core.exceptions.ImproperlyConfigured: Error loading MySQLdb module: No module named ‘M…
- [Solved] error C4430: missing type specifier – int assumed. Note: C++ does not support default-int
- [MacOS Catalina new Shell] How to Solve Error: The default interactive shell is now zsh